Secure IT Infrastructure 79723500 Online

A secure IT infrastructure forms the backbone of any modern organization, particularly in the online domain. It plays a critical role in protecting sensitive data and maintaining operational continuity. Understanding the interplay between risk assessments, identity management, and encryption is essential. However, the landscape of cyber threats continues to evolve. Organizations must adapt their strategies to stay ahead. What measures can effectively counter these emerging challenges?
Understanding the Importance of a Secure IT Infrastructure
While organizations increasingly rely on digital technologies to facilitate operations, the significance of a secure IT infrastructure cannot be overstated.
Effective data protection hinges upon robust security measures that mitigate vulnerabilities. Conducting regular risk assessments allows organizations to identify potential threats, ensuring that their IT framework not only supports operational efficiency but also safeguards sensitive information against breaches and unauthorized access.
Key Components of a Robust Online Security Strategy
To ensure comprehensive protection against cyber threats, organizations must implement several key components within their online security strategy.
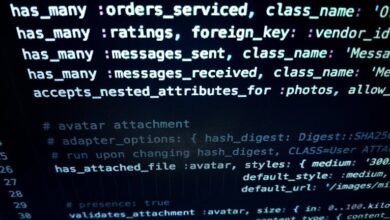
Effective identity management frameworks are essential for verifying user authenticity, while robust encryption techniques safeguard sensitive data during transmission and storage.
Together, these components create a fortified defense, enabling organizations to uphold privacy and security, thus allowing them to navigate the digital landscape with confidence and freedom.
Common Cyber Threats and How to Mitigate Them?
Although the digital landscape continues to evolve, the prevalence of common cyber threats poses significant challenges for organizations seeking to protect their assets.
Phishing attacks and malware remain prevalent, exploiting human vulnerability and system weaknesses.
Effective mitigation strategies include implementing robust malware protection solutions and conducting regular cybersecurity training to enhance employee awareness, thereby reducing the likelihood of successful attacks and safeguarding sensitive information.
Best Practices for Maintaining a Secure IT Environment
The prevalence of cyber threats necessitates a proactive approach to maintaining a secure IT environment.
Effective password management, including the use of multifactor authentication, is essential to safeguard user credentials.
Additionally, implementing network segmentation restricts access, minimizing potential attack surfaces.
These best practices collectively enhance security posture, allowing organizations to operate with greater freedom while reducing vulnerabilities inherent in modern IT infrastructures.
Conclusion
In conclusion, a secure IT infrastructure is crucial for organizations, akin to a fortified castle protecting its inhabitants from external threats. By integrating comprehensive risk assessments and robust security measures, businesses can effectively safeguard sensitive data against evolving cyber threats. The implementation of key components, such as identity management and encryption techniques, serves as a bulwark against unauthorized access. Adopting best practices ensures a resilient environment, enabling organizations to thrive securely in an increasingly digital landscape.